Cryptographic Services Management on Solaris
The Solaris Cryptographic Framework provides cryptographic services to users and applications through commands, a user-level programming interface, a kernel programming interface, and user-level and kernel- level frameworks. The Solaris Cryptographic Framework provides these cryptographic services to applications and kernel modules in a manner seamless to the end user, and brings direct cryptographic services, like encryption and decryption for files, to the end user.
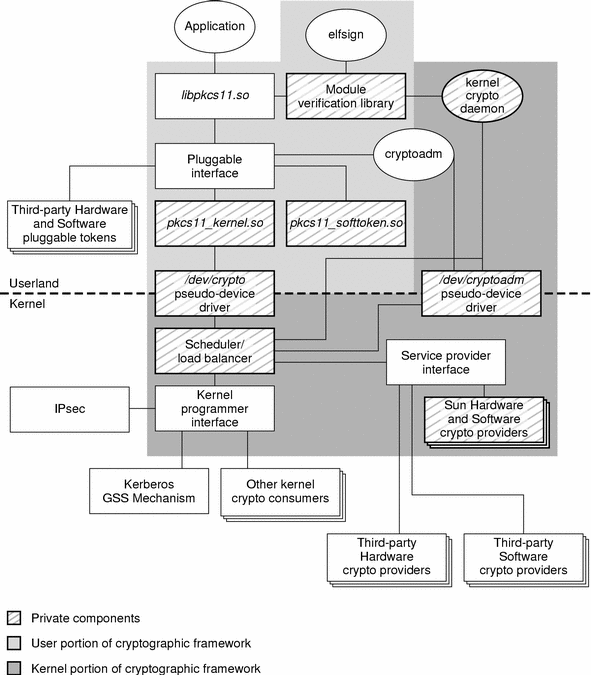
The following diagram is an illustration of the Solaris Cryptographic Framework:
Command-line Utilities
The Solaris Cryptographic Framework includes a number of command-line utilities such as:
encrypt(decrypt). This utility encrypts (decrypts) the given file or content from stdin using the algorithm specified. For more information on these utilities, see encrypt(1) and decrypt(1).digest. This utility calculates the message digest of a given file, set of files, or from stdin using the algorithm specified. For more information on this utility, see digest(1).mac. This utility calculates the message authentication code (MAC) of a given file, set of files, or from stdin using the algorithm specified. For more information on this utility, see mac(1).Administration
In addition, the Solaris Cryptographic Framework includes the cryptoadm(1M) command that displays cryptographic provider information for a system, configures the mechanism policy for each provider, and installs (or uninstalls) a cryptographic provider. The cryptographic framework supports three types of providers: a user-level provider (a PKCS#11 shared library), a kernel software provider (a loadable kernel software module), and a kernel hardware provider (a cryptographic hardware device).
In the following example, the software and hardware implementations of the MD5 algorithm are disabled. The first command impacts the kernel MD5 provider whereas the second command impacts the user-land software MD5 provider:
# cryptoadm disable provider=md5 mechanism=CKM_MD5 # cryptoadm disable \ provider=/usr/lib/security/\$ISA/pkcs11_softtoken_extra.so \ mechanism=CKM_MD5 # digest -v -a md5 /usr/bin/ls digest: no cryptographic provider was found for this algorithm — md5 # cryptoadm list -p User-level providers: ===================== /usr/lib/security/$ISA/pkcs11_kernel.so: all mechanisms are enabled. /usr/lib/security/$ISA/pkcs11_softtoken_extra.so: all mechanisms are enabled, except CKM_MD5. random is enabled. Kernel software providers: ========================== des: all mechanisms are enabled. aes256: all mechanisms are enabled. arcfour2048: all mechanisms are enabled. blowfish448: all mechanisms are enabled. sha1: all mechanisms are enabled. sha2: all mechanisms are enabled. md5: all mechanisms are enabled, except CKM_MD5. rsa: all mechanisms are enabled. swrand: random is enabled. Kernel hardware providers: ==========================
This type of policy configuration could be used, for example, to enforce the use of FIPS 180-2 algorithms by prohibiting the Solaris Cryptographic Framework from supporting algorithms such as MD5.
Resources
For more information, see:
- OpenSolaris Community Project: Cryptographic Framework http://www.opensolaris.org/os/community/security/projects/ef/
- OpenSolaris Community Project: Key Management Framework http://www.opensolaris.org/os/project/kmf/
- Solaris Cryptographic Framework http://www.sun.com/bigadmin/features/articles/crypt_framework.html
- Sun BluePrint: Using the Cryptographic Accelerator of the UltraSPARC T1 Processor http://www.sun.com/blueprints/0306/819-5782.pdf
